Evolution in Cybersecurity Threats: Insights from the Frontlines
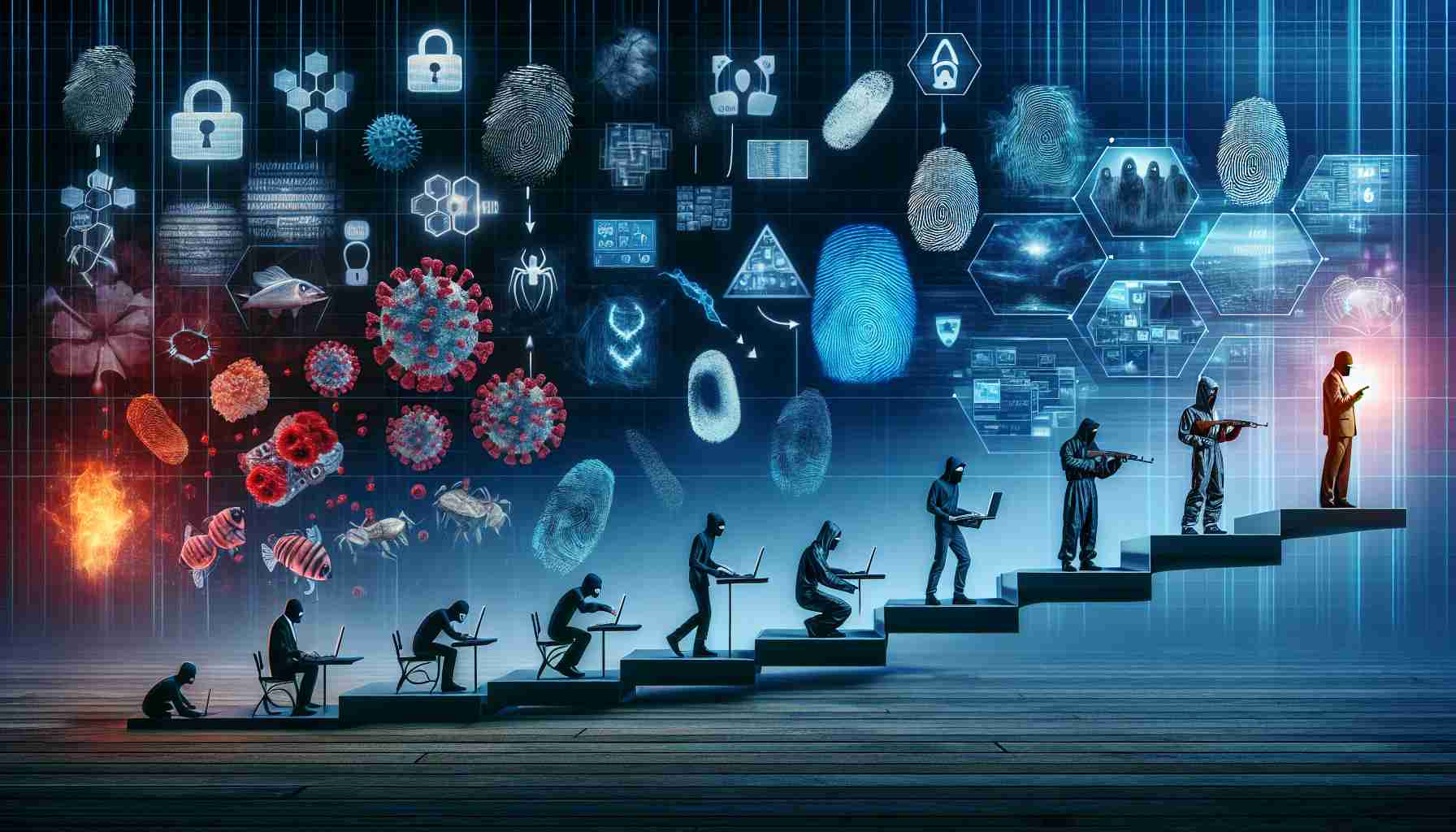
In a recent development, ANY.RUN faced a cyber threat that triggered a chain of sophisticated phishing attacks. Instead of direct quotes from the CEO, let’s delve into the aftermath of the incident. The attack emerged as a wake-up call for organizations worldwide, underscoring the pressing need for robust security measures against evolving cyber threats.
ANY.RUN’s proactive response included uncovering 72 deceptive domains aiming to steal sensitive login information through authentic-looking websites. By analyzing intricate phishing techniques, the company shed light on the importance of tech-savvy vigilance in safeguarding digital assets.
Following the breach, ANY.RUN laid out an enhanced roadmap for upcoming releases, marking a decisive shift towards user-friendly cybersecurity solutions. Innovations such as the comprehensive URL analysis tool and the enriched sandbox environment signify a strategic pivot towards empowering users of all backgrounds to combat modern cyber threats effectively.
This incident underscores the critical role of continuous innovation and collaboration in the cybersecurity landscape. As the digital realm grows increasingly complex, staying ahead of adversaries necessitates adaptive strategies and iterative advancements in defensive capabilities. Stay tuned for a safer digital future with ANY.RUN’s cutting-edge security offerings.
FAQ Section:
1. What cyber threat did ANY.RUN face recently?
– ANY.RUN faced a cyber threat that triggered a chain of sophisticated phishing attacks, highlighting the importance of robust security measures.
2. How did ANY.RUN respond to the incident?
– ANY.RUN responded proactively by uncovering 72 deceptive domains involved in stealing sensitive login information and enhancing their cybersecurity solutions.
3. What innovations did ANY.RUN introduce following the breach?
– ANY.RUN introduced innovations such as a comprehensive URL analysis tool and an enriched sandbox environment to empower users in combating modern cyber threats effectively.
4. What is the significance of continuous innovation in cybersecurity?
– Continuous innovation is critical in staying ahead of adversaries in the cybersecurity landscape and requires adaptive strategies to defend against evolving threats.
Definitions:
1. Phishing: A type of cyber attack where attackers trick individuals into providing sensitive information such as login credentials by masquerading as a trustworthy entity.
2. Vigilance: The action of keeping careful watch for possible dangers or difficulties, especially in the context of cybersecurity, to prevent potential attacks.
3. Sandbox Environment: A secure isolated testing environment within which untrusted programs or files can be executed without affecting the actual system.
Suggested related link:





